Intel GPU passthrough for Ubuntu VM running on VMware vSphere 8
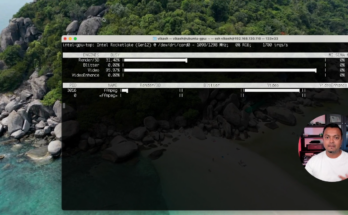
In this video, I will show you how to set up GPU passthrough for an Intel GPU for a Ubuntu virtual machine running on VMware vSphere 8. This way you can use the performance that GPU has for transcoding, encoding, or decoding large video files without stressing the CPU on your VMware ESXi host.
Official documentation from Intel to install graphics drivers on Ubuntu can be found here. Below are all the commands I used to install the drivers on my Ubuntu virtual machine:
sudo apt-get update sudo apt-get install -y gpg-agent wget wget -qO - https://repositories.intel.com/gpu/intel-graphics.key | \ sudo gpg --dearmor --output /usr/share/keyrings/intel-graphics.gpg echo "deb [arch=amd64 signed-by=/usr/share/keyrings/intel-graphics.gpg] https://repositories.intel.com/gpu/ubuntu jammy/production/2328 unified" | \ sudo tee /etc/apt/sources.list.d/intel-gpu-jammy.list sudo apt-get update wget -qO - https://repositories.intel.com/gpu/intel-graphics.key | \ sudo gpg --dearmor --output /usr/share/keyrings/intel-graphics.gpg echo "deb [arch=amd64 signed-by=/usr/share/keyrings/intel-graphics.gpg] https://repositories.intel.com/gpu/ubuntu jammy unified" | \ sudo tee /etc/apt/sources.list.d/intel-gpu-jammy.list sudo apt-get update sudo apt-get install -y intel-i915-dkms xpu-smi sudo reboot -h now sudo apt-get install -y \ intel-opencl-icd intel-level-zero-gpu level-zero \ intel-media-va-driver-non-free libmfx1 libmfxgen1 libvpl2 \ libegl-mesa0 libegl1-mesa libegl1-mesa-dev libgbm1 libgl1-mesa-dev libgl1-mesa-dri \ libglapi-mesa libgles2-mesa-dev libglx-mesa0 libigdgmm12 libxatracker2 mesa-va-drivers \ mesa-vdpau-drivers mesa-vulkan-drivers va-driver-all vainfo hwinfo clinfo sudo apt-get install intel-gpu-tools sudo reboot -h nowIntel GPU passthrough for Ubuntu VM running on VMware vSphere 8 Read More