Table of Contents
I’m a big fan of Pi-hole and have been using it to get rid of advertisement and tracking. Check my blogpost here if you want to know how to set Pi-hole up. It’s an amazing piece of software to protect your online privacy and provide network wide ad-blocking. In my day job I’m an IT-consultant for enterprise IT-solutions and in this post I will show you how to use Pi-hole with Microsoft Active Directory and protect all your domain joined clients from advertisement, tracking and also keep your clients secure from those malware websites.
Of course, you need to test this extensively before rolling it out in your infrastructure. I cannot stress this enough. The solution described in this blogpost did not show any kind of strange unexpected behaviour in my testlab but every infrastructure is different. Especially with endusers and applications there may be some challenges. So test before you implement!
Requirements
Microsoft Active Directory depends on Active Directory-Integrated DNS Service and Active Directory-Integrated DHCP Service. In this scenario all your domain joined clients are getting their IP-addresses and DNS settings from the Microsoft DHCP server. The DNS settings is used by the domain joined clients to talk to the Active Directory for DNS lookups and Active Directory related tasks. My testlab is running on Windows Server 2019 Active Directory and DNS Service, but this should also work if you are running a Windows Server 2016 environment. The requirement list is:
- Microsoft Windows Server 2019
- Microsoft Active Directory 2019
- Microsoft Active Directory-Integrated DNS 2019
- Microsoft Active Directory-Integrated DHCP Server 2019
- Pi-hole Server
- Domain joined client(s)
Let’s get started
They key Pi-hole feature we will be using in order to get this working is called Conditional Forwarding. I will explain in this post later on how we will use this feature.
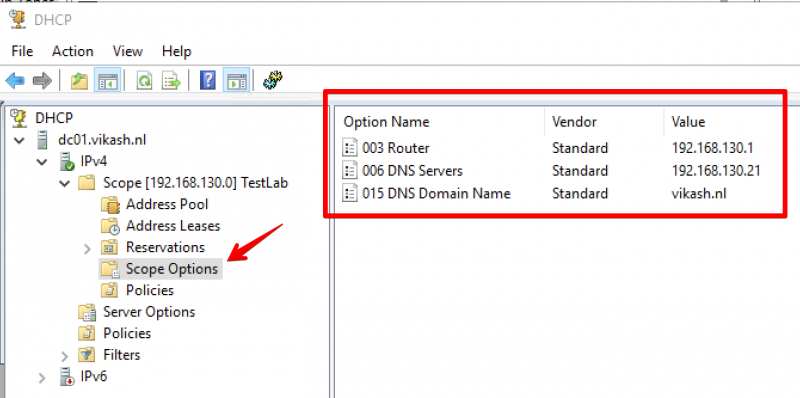
DHCP Server settings
My DHCP Server is running on my Active Directory Domain controller. I’m sure a lot of you have the same setup which is fine. In the DHCP Server we have to specify certain options like DNS Servers and DNS Domain Name. My DHCP server is running on IP-address 192.168.130.10. My DNS Domain Name is vikash.nl. For DNS Servers fill in the IP-address of your Pi-hole Server. My Pi-hole server is running on IP-address 192.168.100.21.
On your DHCP server open the management console for DHCP Server and expand the scope options. Make sure the values match your network infrastructure:
Pi-hole Server settings
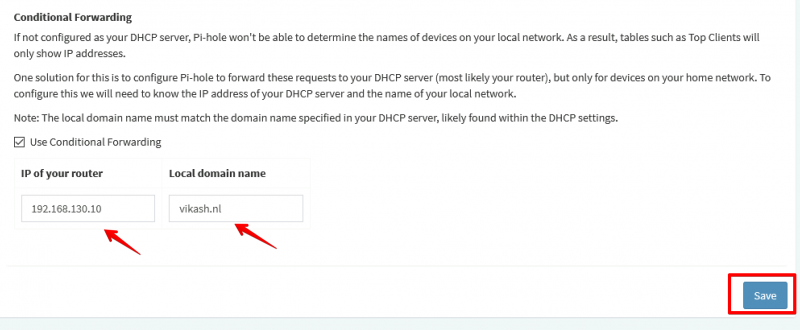
Now I will show you how to use Pi-hole with Microsoft Active Directory. The idea here is provide the Pi-hole Server as the DNS server to your domain joined clients. Then in the Pi-hole Server settings we will enable the option called Conditional Forwarding. Here we have to enter the IP-address of our Active Directory-Integrated DHCP server and also a Local Domain Name. This local domain name has to be your Active Directory name. In my case that is vikash.nl. What will happen now is that if the Pi-hole gets DNS requests from clients that need to resolve something.vikash.nl it will forward that request to our DHCP server which is also our Active Directory Domain controller. This makes sure that all the Active Directory related communications between my domain joined clients and Active Directory are completed successfully.
On the Pi-hole server go to Settings and select the DNS tab:
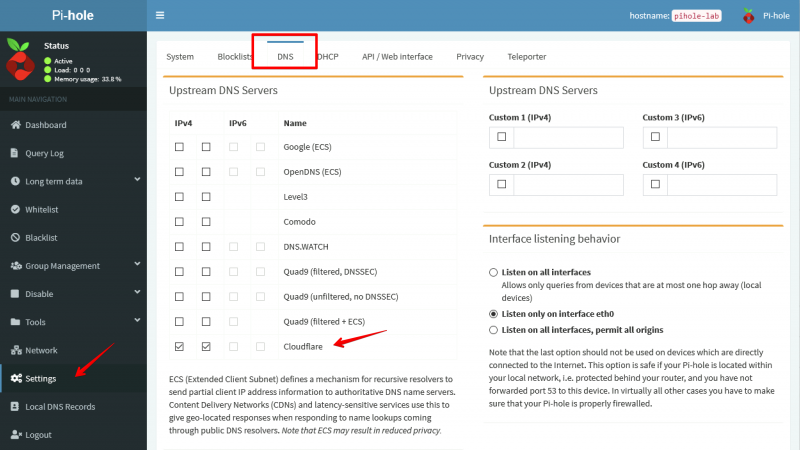
As you can see in the screenshot above I am using Cloudflare DNS Servers as my Upstream DNS. You can use any DNS Server as your upstream DNS. This basically means that for all DNS requests not related to vikash.nl the Pi-hole server will resolve those using Cloudflare. That is exactly what we want because it will make sure that internet is still working for all our domain joined clients. At the same time we will be able to see all the DNS requests in the Pi-hole Server Query Log for every client. This gives us control to protect our domain joined clients from ads, tracking or even malware.
In the DNS tab scroll to the bottom of the page and enter the DHCP server IP-address and the Local Domain Name. My DHCP server is 192.168.130.10 and my Local Domain Name is vikash.nl. Check your network infrastructure for your specific settings and click Save:
Testing
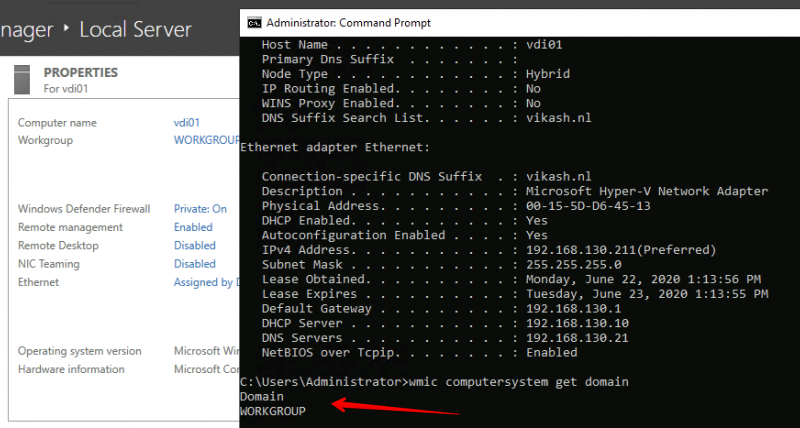
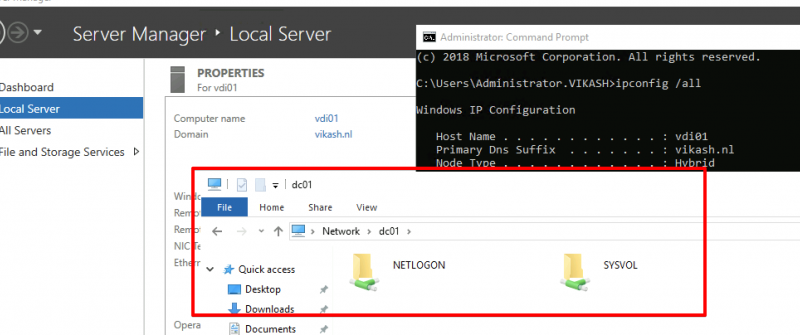
Now let’s make sure that everything works. First we will check that the correct DHCP settings are distributed to a client we want to join to the domain vikash.nl. I will use a Windows Server 2019 as client with the name vdi01.
Check IP-address
Open up a command prompt on the machine and make sure that the client is getting the correct settings from the DHCP server:
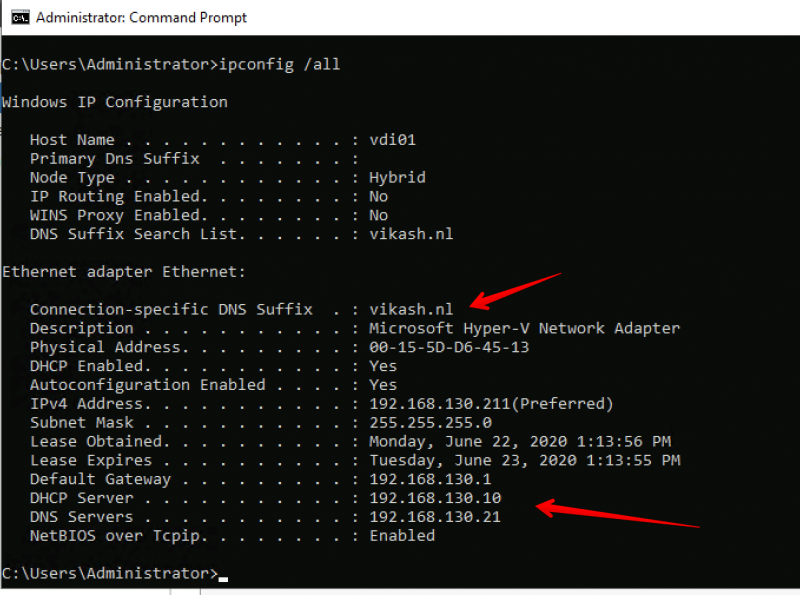
As you can see in the screenshot above the client is getting the DNS Domain Name and the DNS Server settings according to our scope options in the DHCP server. Check that the client is not already domain joined:
Join the client to the domain
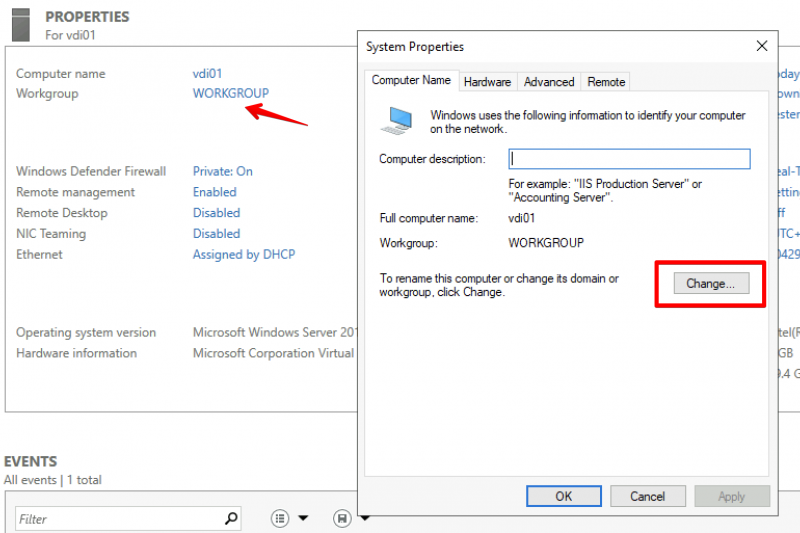
Next step is to join the client (my vdi01) to my domain vikash.nl. Click in the Server Manager on WORKGROUP and then click on Change in the window that pops up:
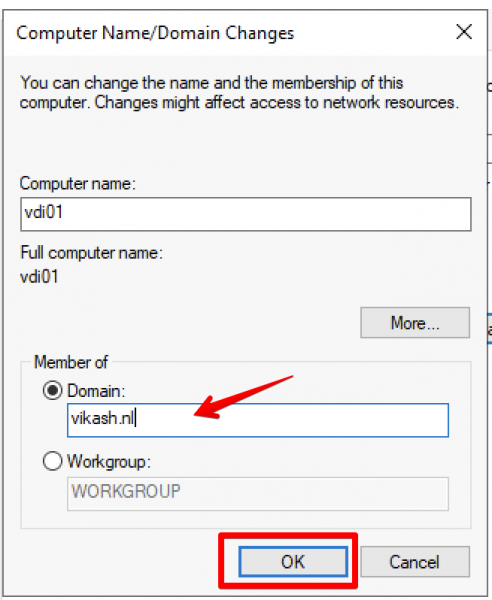
Select the Domain option here and enter your domain name. Remember that this must be the same as DNS Domain Name entered in the DHCP Scope options and in the Conditional Forwarding on the Pi-hole. In my case this is vikash.nl. Then click on OK.
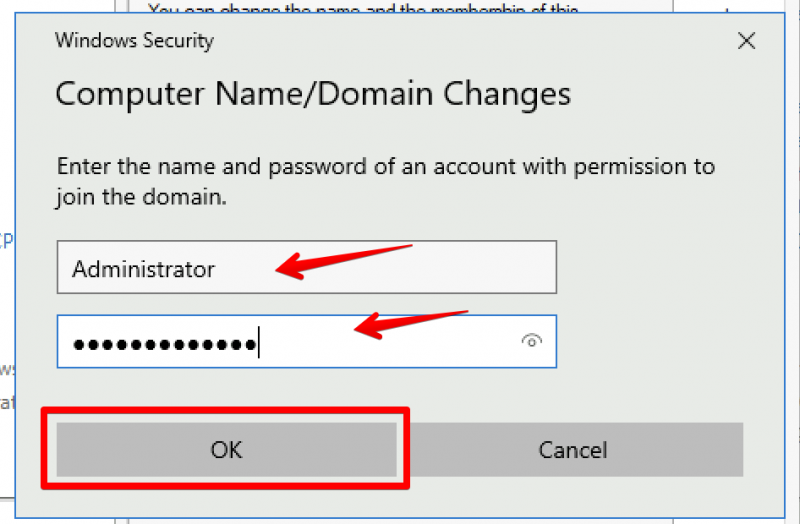
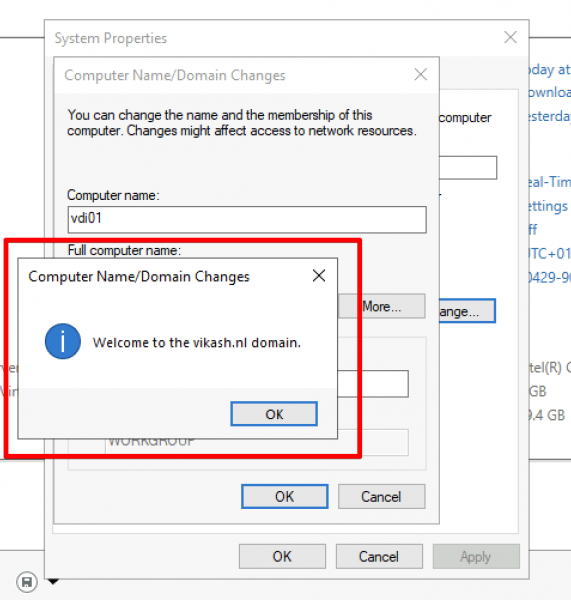
Windows will prompt you to enter Domain credentials which are allowed to do a domain join. In my testlab I use the domain administrator account for that. Enter the credentials and click on OK:
You will get a prompt from Windows telling you that the domain join was completed successfully. It looks like everything is working :). Click on OK and reboot you client.
After the client reboots login using a domain account:
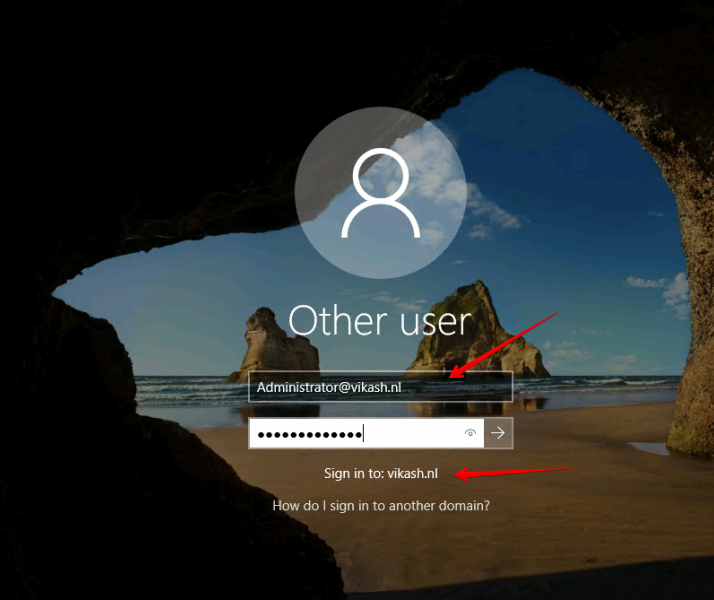
Check that everything is ok and the client is a member of the domain:
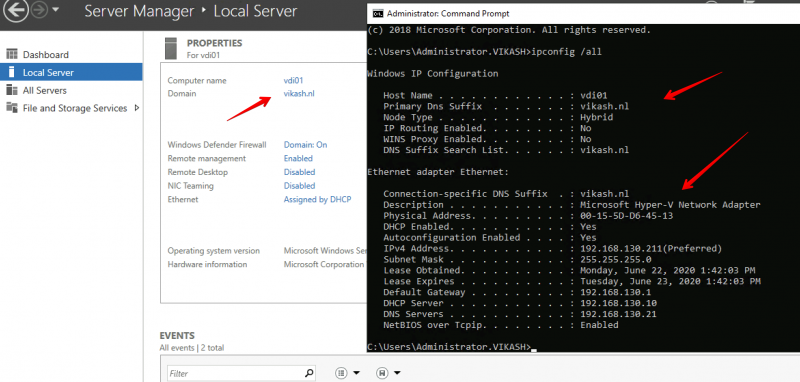
Check Pi-hole Query Log
We can see the magic happening when we check the Query Log on our Pi-hole Server. Open the admin page of Pi-hole server and select the Query Log in the left menu:
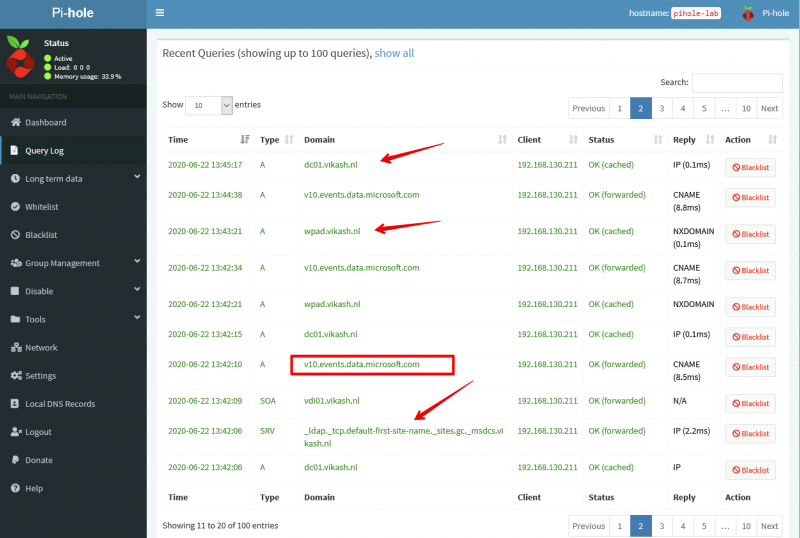
As you can see in the screenshot above my client with IP-address 192.168.130.211 (vdi01.vikash.nl) is able to resolve internet queries as wel as queries related to my domain vikash.nl. Filesharing is working fine as well:
How amazing is this?! We are using Pi-hole with Microsoft Active Directory infrastructure and that means that we can now benefit from the protection of Pi-hole on enterprise level :). Of course this test is limited but imagine the possibilities. You can now provide all your endusers with a ad-free and tracking free internet experience but still be in control if some specific website needs to be unblocked.


The problem with this architecture is that you have now lost the benefits of AD integration with DNS, and dynamic DNS updates.
A simpler and better approach is to leave the MS DHCP & DNS servers in place, and simply configure the MS DNS server(s) to point to PiHole for non-local name resolution (i.e. replace root hints in the MS DNS with lookup forwarding. The forwarding DNS server is your piHole.)
Hi and thanks for the feedback! Yes that is another way of integrating Pi-hole. But then you will loose the client ip information because all the requests will be coming from the MS DNS. In the end it depends on the infrastructure and what you are trying to achieve.
loose the client info from which location? pihole or MS DNS mgr.
Hi. Depends on what DNS server the clients are using and your specific network design. I can imagine that windows will need the Windows DNS server for specific this. Again, test extensively before implementing.
Hi Ross,
is there a way to keep the dynamic updates on the AD-DNS and at the same time see the IP information on the Pi-hole
Regards
how to use pi-hole with public ip (publish on internet) so i can use on mobile device as dns or any other systems.
Hi,
First of all Pihole is not meant to be exposed to the internet! Don’t do it :). But if you must use your own Pihole I would suggest to set something up like Wireguard VPN. Then when you are not at home (where your Pihole is) you can just simply VPN from your mobile device to your network and in that way use Pihole. There are a lot more solutions to achieve what you want in the end. Goodluck!
Utilizing Wireguard VPN with PiHole works fairly well for me when i am not home. My configuration has Pi-Hole and Wireguard VPN on the same machine. This allows PiHole to simply monitor the internal network and the Wireguard VPN network. It works very well.
In PiHole, Settings section, DNS tab, select under the Interface listening behavior, Listen on all interfaces. This allows PiHole to listen on the internal network and Wireguard VPN network
simple question , AD and pihole dhcp and dns
why is not the same, will not accept to build a windows DC around this?
missing service records and so on
it works until you want to ad an windows 2019 DC to it….
Hi! Yes you have to test it for your specific situation. Of course you can just point all your clients to the Windows DNS and forward all the DNS queries to Pihole.
I miss the picture , would like to have one raspberry dchp and dns server so my smart… systems no windows systems can run 24/7 . But at the moment I power on my testlab with esxi … I would love to have this raspberry dhcp/dns AD to accept / deal with what I run on my esxi test systems and all dynamic please. so I don’t want to add for every vm static …
regards
Rick
I have no idea what your specific question is but you can just use your DHCP server (being it your router or pihole) to distribute DNS servers to clients. Should be no problem for ESXi to get the correct DNS server from your router.
Hello Vikash ,
Any progress on: Is there a way to keep the dynamic updates on the AD-DNS and at the same time see the client IP information on the Pi-hole query log as opposed to the MS DNS being logged?
Good question. I suppose it should be possible but I have not tested this my self because I have no need for it :).
Simply set up your DNS server with the pi-hole on your AD client. If you have setup the DNS Conditional Forwarding correctly on your pi-hole, all query to your local domain will be sent to your AD DNS and dynamic update will works.
Hello,
could you please explain why it is important that the clients join the domain after the settings are all done. Wouldn’t a simple ipconfig /renew on every client be enough?
Greetings
Hi. For AD domain functions it is important that the clients can reach the AD DNS.
on the DNS snapin for all the domain controllers what do you do there for Forwarders do you just leave that blank? OR put in pihole IP’s there, technically those should be blank yes?
Yes they should be blank because they rely on the AD. Test it and see how that goes. You can always manually point the DC’s to you PDC.
I have been going round and round with the proper setup configs for piHole with AD but I have not found a solution that fits the bill 100%.
I use MS DHCP and MS DNS on 2 Server 2022 DC’s. I have all my clients pointed to my AD DNS servers (for proper AD use). I have configured the forwarders on each MS DNS to point to my piHole and have unchecked the “Use Root hints if no forwarders are available” box. piHole itself is configured to use IPv4 Quad9 (filtered, DNSSEC) servers and I do not have “Use Conditional Forwarding” enabled. In this config, the MS DNS servers get the query and then ask piHole. piHole in turn askes Quad9.
I have several problems with this setup. 1st… the piHole is a single point of failure. if it’s down, nothing external will resolve. I could stand up an another piHole and for redundancy and that would solve the 1st problem. 2nd… I loose the ability to independently configure rules in piHole for each host because right now, all the requests coming into piHole is from my 2DC’s. I would love to be able to create groups and use the blocking functionality on a per host basis. right now its all or nothing.
There is an option to have multiple piholes running configured with sync. I have not tested that because I don’t need it, but there are others who have successfully set this up. For the other part the pihole need to be able to see the host ip’s so that won’t work unfortunately.
Has anyone tried with a hardcoded DNS (E.g. 8.8.8.8, etc.) on the client?
You’ll have to find a way to intercept those DNS requests and re-route them to pihole. This depends on the capabilities of your firewall/router.